OTP 101: The ins and outs of one-time passwords
Breaches drive enterprises to both hardware and software tokens
29 May, 2014
category: Corporate, Digital ID, Financial, Health
By Will Rodger, Contributing Editor
Faced with relentless attacks by high-powered hackers, hardware and software makers are increasingly turning their attention to passwords that can be generated on the fly, used once and then discarded forever. Once thought to be overkill for all but the most sensitive data, mainstream users are picking up on the technology at a pace unforeseen just a few years ago.
“The strengths are simple,” says independent security professional Peter Wayner. “Changing the password prevents a host of problems created by key loggers, eavesdropping, shoulder surfing and viruses. That’s a big win because those are some of the most common threats today.”
How OTP works
One-time-password technologies rely on a token or server separate from the user’s computer. One-time-password solutions, by definition, rely on at least two information sources and thus are a form of multi-factor authentication. Whatever the specifics, an attacker has to compromise all the inputs simultaneously. Because of this, most adversaries find the task impossible today.
Here’s one example in action. Plastic hardware tokens typically hang from key rings and include small LCD screens that spit out random pass codes. Those passwords will change every 30 seconds or so in synchronization with a server that calculates the same number tied to the user. The combination of something the user knows (a PIN) and something he has — the token’s pass code — makes compromise very difficult.
As with everything in computing, there are drawbacks. While most experts agree that hardware tokens are among the most secure approaches right now, they are also bulky, expensive and typically single-function, tied to only one system at a time.
Going Soft
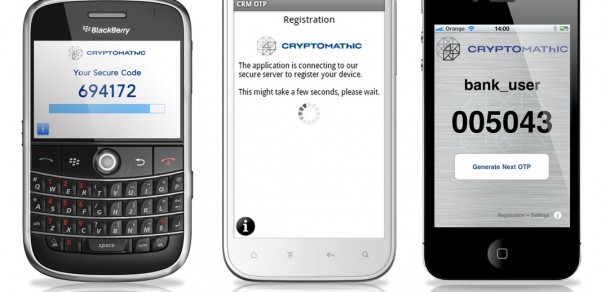
In their place are the increasingly popular “soft tokens,” or authentication systems that rely on tablets, laptops, desktops and smartphones to produce the passwords traditionally generated by stand-alone hardware tokens. Some systems even do the math on the server end, sending passwords back to the user.
For obvious reasons, the smart phone piece of the market has taken off. While PINS are still one way to verify identity using a smart phone, handheld computers can now accept more and better factors than most PCs by virtue of all the sensors and technologies on board. Integrated cameras can pick up iris and face prints; motion sensors can demand a distinctive shake from their owners; and GPS and IP ports can pinpoint a user’s location. Likewise, the iPhone 5S has famously added a fingerprint scanner to its main control button.
Verizon is sold on the value of multi-platform approaches, explains Peter Graham, senior identity strategist at Verizon Enterprise Solutions. The company’s Universal Identification Service is a fully managed cloud-based authentication and ID proofing platform that can handle everything from ID issuance all the way through NIST Level 3 security requirements.
To sign up, users log in from a secure site or use an agreed-upon form of third-party ID to log into a site that is running the Verizon platform.
Let’s say a physician wants to prescribe narcotics remotely, Graham explains. To do that, he can set up an account online using a digital certificate issued to him by the SAFE-BioPharma Association. The Universal Identification Service gives him a username and PIN sent through an encrypted browser session in return.
The physician can now use that username and PIN — something he knows — to obtain a password that will remain valid for only 30 seconds.
Because usernames and PINs can be guessed, Graham says Verizon adds something he has to the mix. If he has a cellphone, Verizon can send an SMS message with the password he needs. If he has a PC, smart phone, tablet or other screened device, the company can send a message to a proprietary bit of software — a soft token — instead. They can even ring landlines to deliver one-time passwords.
“As smart platforms get more secure and as the standards get a lot tighter, more and more people will enable their employees and customers to use the devices they have,” says Tracy Hulver, chief identity strategist at Verizon Enterprise Solutions. “It’s more convenient and a heck of a lot cheaper for the company that wants to roll out stronger authentication in a secure way.”
Making a choice
So how do you choose? First you need to determine the importance of the information you want to protect. If it’s not that important, you may not be able to justify the budget to secure it.
It’s also crucial to know who will be accessing the information you want to secure. The technology chosen has to not only be affordable, but also scalable and simple enough for the intended audience.
The company’s CFO and general counsel, for instance, may be happy typing in long, cumbersome passwords from a key fob when they have to handle sensitive documents. The larger user base with Android devices prone to phishing attacks and click-bait are likely the greater risk.
Additionally, there’s little chance that networked retail customers will mess with a physical token, so you have to figure out what they will tolerate.